Stunnel howto
Содержание:
Step 4: Configure Stunnel on the VPS
Stunnel configures itself using a file named “stunnel.conf” which by default is located in “/etc/stunnel”.
Create a “stunnel.conf” file in the “/etc/stunnel” directory:
We’re going to be using a SSL certificate to identify ourselves to the server so we have to set the path to that certificate in “stunnel.conf” file using this line (We will create the certificate file in the next step):
Next we specify a service for use with Stunnel. It can be any of the services which use networking such as mail server, proxy server, etc.
Here as an example we’re going to secure traffics between Squid proxy server and a client using Stunnel. We’ll explain how to install and configure Squid in Step 6.
After setting a name for the service you’re going to use, you must tell Stunnel to listen on which port for that service. This can be any of the 65535 ports, as long as it’s not blocked by another service or firewall:
Then depending on the service you’re going to use the secure tunnel on, you must specify the port and IP address of that in the configuration file Basically Stunnel takes packets from a secure port and then forwards it to the port and IP address of the service you specified.
Squid proxy by default runs on localhost and port 3128 so we have to tell Stunnel to forward accepted connections to that port:
connect = 127.0.0.1:3128
So overall the “stunnel.conf” file must contain the lines below:
Note: The part isn’t necessary, Stunnel by default is set to server mode.
Installation
This section gives you basic information on how to run the stunnel program in client and server mode.
Running stunnel in inetd mode
(This does not apply to Windows machines)
You can invoke stunnel from . Inetd is the Unix ‘super server’ that allows you to launch a program (for example the telnet daemon) whenever a connection is established to a specified port.
Lets say we want to have stunnel listen on our machine on port to support a fictitious protocol called . We would add the following line to the file
(if you installed stunnel in a different location than , use that path instead) and add the following line to :
You must then send the process a . Find the process id for the process by one of the following commands:
and then type .
You may be able to use on some Unix versions (for example linux, *BSD, IRIX) to save yourself from looking up the process id.
Note: Some Unix variants have a command that kills all processes on the machine. That is not the you are looking for…
The configuration file for mode must not include a line. For example:
If you have a line, then stunnel will fork into the background to do its job, and will not work with inetd.
Note: Running in daemon mode is much preferred to running in inetd mode. Why?
- SSL needs to be initialized for every connection.
- No session cache is possible.
- inetd mode requires forking, which causes additional overhead. Daemon mode will not fork if you have stunnel compiled with threads.
Running stunnel in daemon mode
Lets say we want to have stunnel listen on our machine on port to support a fictitious protocol called .
First we would add the following line to :
Stunnel configuration file needs at least the section name and option. For example:
Running stunnel with TCP wrappers
You do not need to use the tcpd binary to wrap stunnel (although you could). You can can compile in support for TCP wrappers when you compile stunnel itself.
The program should be able to determine if the libwrap library () and headers are available in standard locations.
You must put entries in to specify which machines should be allowed access to . These are of the form:
Service name is the name of service that was put in square brackets in .
Stopping stunnel
If stunnel is running in daemon mode, you can stop it simply by ing it. Stunnel accepts the following signals, all of which tell it to log the signal and terminate: .
Running stunnel as a service under windows
Stunnel can run as a native service under Windows. To install stunnel as a service execute:
in the directory where is available.
Download the Client Files
Next, download these client files which will be used for the setup later. If you have problems with step, research a little on the command.
// These commands are ran on the server to copy files over to /tmp$ cp /etc/openvpn/easy-rsa/keys/ca.crt /tmp$ cp /etc/openvpn/easy-rsa/keys/client1.* /tmp// These scp commands are meant to be ran on your local machine$ scp root@your-hostname:/tmp/ca.crt ~/Downloads$ scp root@your-hostname:/tmp/client1.* ~/Downloads// Clean up after ourselves. Removing what we copied on the server$ rm -rf /tmp/ca.crt$ rm -rf /tmp/client1.*
Setup Stunnel Server + Client
Description
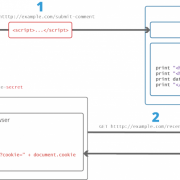
The stunnel program is designed to work as SSL encryption wrapper between remote clients and local (inetd-startable) or
remote servers. The concept is that having non-SSL aware daemons running on your system you can easily set them up to communicate with clients over secure
SSL channels.
stunnel can be used to add SSL functionality to commonly used Inetd daemons like POP-2 , POP-3 ,
and IMAP servers, to standalone daemons like NNTP , SMTP and HTTP , and in tunneling
PPP over network sockets without changes to the source code.
This product includes cryptographic software written by Eric Young (eay@cryptsoft.com)
Что такое stunnel
Stunnel — это утилита для обеспечения защищенного соединения между клиентом и сервером посредством TLS для программ, которые сами шифровать трафик не умеют. Например, можно туннелировать трафик для netcat, vnc и даже bash.
В нашем примере stunnel будет использоваться для маскировки трафика OpenVPN под «чистый» TLS, чтобы его было невозможно определить посредством DPI и, следовательно, заблокировать.
Трафик, туннелируемый через stunnel, ничем не отличается от обычного HTTPS
С учетом того что OpenVPN использует шифрование для своего канала данных, у нас есть два варианта настройки:
- использовать шифрование stunnel плюс шифрование канала данных OpenVPN;
- использовать шифрование stunnel, а шифрование канала данных OpenVPN отключить.
Таким образом, в первом варианте получается два слоя: один от stunnel, второй от OpenVPN. Этот вариант позволит использовать RSA вместе с ECDSA. Недостаток в том, что тратится больше ресурсов, и второй вариант позволит этого избежать. В любом случае настройка stunnel остается неизменной.