Setfacl(1) — linux man page
Содержание:
COLOPHON top
This page is part of the acl (manipulating access control lists)
project. Information about the project can be found at
⟨http://savannah.nongnu.org/projects/acl⟩. If you have a bug report
for this manual page, see
⟨http://savannah.nongnu.org/bugs/?group=acl⟩. This page was obtained
from the project's upstream Git repository
⟨git://git.savannah.nongnu.org/acl.git⟩ on 2020-08-13. (At that
time, the date of the most recent commit that was found in the repos‐
itory was 2020-02-06.) If you discover any rendering problems in
this HTML version of the page, or you believe there is a better or
more up-to-date source for the page, or you have corrections or
improvements to the information in this COLOPHON (which is not part
of the original manual page), send a mail to man-pages@man7.org
May 2000 ACL File Utilities GETFACL(1)
Pages that refer to this page:
chacl(1),
setfacl(1),
tmpfiles.d(5)
Автоматические операции
Любой администратор стремится к оптимизации. Понятно, что назначить вручную 100 объектам одни и те же права — нудное занятие и нецелесообразное. Есть некоторые фишечки, которые могут облегчить подобные задачи.
Копирование ACL прав с одного объекта на другой.
Принцип прост:
- Снять ACL c одного объекта
- Записать их на другой
В документации приведен следующий пример:
getfacl file1 | setfacl --set-file=- file2
Где, file1 — объект с которого снимаем ACL командой getfacl, а далее устанавливаем ACL командой setfacl на объект file2
Обратите внимание на запись — -set-file=- в конце указан символ «-», который берет информацию от команды getfacl (со стандартного вывода)
Справедлива будет также такая запись:
getfacl file1 | setfacl -M- file2
В этом случае права на file2 не заменяются как при использовании — -set, а добавляются к уже существующим правам ACL.
OPTIONS
| Tag | Description |
|---|---|
| —access | |
| Display the file access control list. | |
| -d, —default | |
| Display the default access control list. | |
| —omit-header | |
| Do not display the comment header (the first three lines of each files output). | |
| —all-effective | |
| Print all effective rights comments, even if identical to the rights defined by the ACL entry. | |
| —no-effective | |
| Do not print effective rights comments. | |
| —skip-base | |
| Skip files that only have the base ACL entries (owner, group, others). | |
| -R, —recursive | |
| List the ACLs of all files and directories recursively. | |
| -L, —logical | |
|
Logical walk, follow symbolic links. The default behavior is to follow symbolic link arguments, and to skip symbolic links encountered in subdirectories. |
|
| -P, —physical | |
|
Physical walk, skip all symbolic links. This also skips symbolic link arguments. |
|
| —tabular | |
| Use an alternative tabular output format. The ACL and the default ACL are displayed side by side. Permissions that are ineffective due to the ACL mask entry are displayed capitalized. The entry tag names for the ACL_USER_OBJ and ACL_GROUP_OBJ entries are also displayed in capital letters, which helps in spotting those entries. | |
| —absolute-names | |
|
Do not strip leading slash characters (/). The default behavior is to strip leading slash characters. |
|
| —version | |
| Print the version of getfacl and exit. | |
| —help | |
| Print help explaining the command line options. | |
| — | End of command line options. All remaining parameters are interpreted as file names, even if they start with a dash character. |
| — |
If the file name parameter is a single dash character, getfacl reads a list of files from standard input. |
ACL ENTRIES top
An ACL consists of a set of ACL entries. An ACL entry specifies the
access permissions on the associated object for an individual user or a
group of users as a combination of read, write and search/execute
permissions.
An ACL entry contains an entry tag type, an optional entry tag
qualifier, and a set of permissions. We use the term qualifier to
denote the entry tag qualifier of an ACL entry.
The qualifier denotes the identifier of a user or a group, for entries
with tag types of ACL_USER or ACL_GROUP, respectively. Entries with tag
types other than ACL_USER or ACL_GROUP have no defined qualifiers.
The following entry tag types are defined:
ACL_USER_OBJ The ACL_USER_OBJ entry denotes access rights for
the file owner.
ACL_USER ACL_USER entries denote access rights for users
identified by the entry's qualifier.
ACL_GROUP_OBJ The ACL_GROUP_OBJ entry denotes access rights for
the file group.
ACL_GROUP ACL_GROUP entries denote access rights for groups
identified by the entry's qualifier.
ACL_MASK The ACL_MASK entry denotes the maximum access
rights that can be granted by entries of type
ACL_USER, ACL_GROUP_OBJ, or ACL_GROUP.
ACL_OTHER The ACL_OTHER entry denotes access rights for
processes that do not match any other entry in
the ACL.
When an access check is performed, the ACL_USER_OBJ and ACL_USER
entries are tested against the effective user ID. The effective group
ID, as well as all supplementary group IDs are tested against the
ACL_GROUP_OBJ and ACL_GROUP entries.
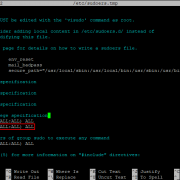
Using Setfacl
First, try setting up a basic list for a folder in your home directory. Since you’re trying this out for the first time, make a new one to play with. This way, you won’t risk locking yourself out of important documents.
mkdir ~/acl-test
Next, use setfacl to grant another user on your system access to the folder. Setfacl uses the -m flag to modify the access control lists for a file. This usually means adding a user or group.
setfacl -m u:username:rwx ~/acl-test/
The u before the first colon tells the command you’re talking about a username. The rwx following the second one grants read, write, and execute permissions.
The same works for groups by specifying g instead of u before the first colon.
setfacl -m g:groupname:rwx ~/acl-test/
It works the same as the previous example, except that it grants permissions to the entire group.
The -x flag works the opposite of -m. It will revoke access to the specified user or group.
setfacl -x u:username:w ~/acl-test/
The command revokes write access to the directory to the user.
You can also directly modify the permissions for all current users. This includes the owner of the file and any additional users that were granted permissions. This is something of a shortcut, using the existing command but omitting the username.
setfacl -m u::rx ~/acl-test/
This grants all existing users read and execute permissions but removes write access.
The same works with the -x flag and removing permissions.
setfacl -x u::w ~/acl-test/
This is essentially the same as the previous example, inverted.
setfacl also lets you copy the access control lists from one file to another. Make sure that your user has full access to the test folder, and create two new files to work with.
touch ~/acl-test/file{1,2}.txt
Now, modify the permissions of the first file.
setfacl -m u:username:rx ~/acl-text/file1.txt
Now, you can pipe the results of getfacl, the command for retrieving the current ACL info, into setfacl.
getfacl ~/acl-test/file1.txt | setfacl --set-file=- ~/acl-text/file2.txt
The second fill will have the same permissions as the first.
Finally, you can remove all extended ACL entries created by the command. This will leave the file with the user and group permissions that it originally had. To do this, use the -b flag.
setfacl -b ~/acl-test/
Those are the most common uses of setfacl. If you want to dive deeper, the next portion of this guide is a complete technical breakdown of the command.
Description
For each file, getfacl displays the file name, owner, the group, and the Access Control List (ACL). If a directory has a default ACL, getfacl also displays the default ACL. Non-directories cannot have default ACLs.
If getfacl is used on a file system that does not support ACLs, getfacl displays the access permissions defined by the traditional file mode permission bits.
The output format of getfacl is as follows:
1: # file: somedir/ 2: # owner: lisa 3: # group: staff 4: user::rwx 5: user:joe:rwx #effective:r-x 6: group::rwx #effective:r-x 7: group:cool:r-x 8: mask:r-x 9: other:r-x 10: default:user::rwx 11: default:user:joe:rwx #effective:r-x 12: default:group::r-x 13: default:mask:r-x 14: default:other:---
Lines 4, 6 and 9 correspond to the user, group and other fields of the file mode permission bits. These three are called the base ACL entries. Lines 5 and 7 are named user and named group entries. Line 8 is the effective rights mask. This entry limits the effective rights granted to all groups and to named users. (The file owner and others permissions are not affected by the effective rights mask; all other entries are.) Lines 10 through 14 display the default ACL associated with this directory. Directories may have a default ACL. Regular files never have a default ACL.
The default behavior for getfacl is to display both the ACL and the default ACL, and to include an effective rights comment for lines where the rights of the entry differ from the effective rights.
If output is to a terminal, the effective rights comment is aligned to column 40. Otherwise, a single tab character separates the ACL entry and the effective rights comment.
The ACL listings of multiple files are separated by blank lines. The output of getfacl can also be used as input to setfacl.
Description
For each file, getfacl displays the file name, owner, the group, and the access control list. If a directory has a default ACL, getfacl also displays the default ACL. Non-directories cannot have default ACLs.
Getty Images/John Coulter
If getfacl is used on a file system that does not support ACLs, getfacl displays the access permissions defined by the traditional file-mode permission bits.
The output format of getfacl is as follows:
1: # file: somedir/ 2: # owner: lisa 3: # group: staff 4: user::rwx 5: user:joe:rwx #effective:r-x 6: group::rwx #effective:r-x 7: group:cool:r-x 8: mask:r-x 9: other:r-x10: default:user::rwx11: default:user:joe:rwx #effective:r-x12: default:group::r-x13: default:mask:r-x14: default:other:---
Lines 4, 6 and 9 correspond to the user, group and other fields of the file mode permission bits. These three are called the base ACL entries. Lines 5 and 7 are named user and named group entries. Line 8 is the effective rights mask. This entry limits the effective rights granted to all groups and to named users. (The file owner and others permissions are not affected by the effective rights mask; all other entries are.) Lines 10 through 14 display the default ACL associated with this directory. Directories may have a default ACL. Regular files never have a default ACL.
The default behavior for getfacl is to display both the ACL and the default ACL and to include an effective rights comment for lines where the rights of the entry differ from the effective rights.
If the output is to a terminal, the effective rights comment is aligned to column 40. Otherwise, a single tab character separates the ACL entry and the effective rights comment.
The ACL listings of multiple files are separated by blank lines. The output of getfacl can also be used as input to setfacl.
DESCRIPTION
If getfacl is used on a file system that does not support ACLs, getfacl
displays the access permissions defined by the traditional file mode permission
bits.
The output format of getfacl is as follows:
-
1: # file: somedir/ 2: # owner: lisa 3: # group: staff 4: # flags: -s- 5: user::rwx 6: user:joe:rwx #effective:r-x 7: group::rwx #effective:r-x 8: group:cool:r-x 9: mask::r-x 10: other::r-x 11: default:user::rwx 12: default:user:joe:rwx #effective:r-x 13: default:group::r-x 14: default:mask::r-x 15: default:other::---
Lines 1—3 indicate the file name, owner, and owning group.
Line 4 indicates the setuid (s), setgid (s), and sticky (t) bits: either
the letter representing the bit, or else a dash (-). This line is
included if any of those bits is set and left out otherwise, so it will
not be shown for most files. (See CONFORMANCE TO POSIX 1003.1e DRAFT STANDARD~17
below.)
Lines 5, 7 and 10 correspond to the user, group and other fields of
the file mode permission bits. These three are called the base ACL
entries. Lines 6 and 8 are named user and named group entries. Line 9 is
the effective rights mask. This entry limits the effective rights granted
to all groups and to named users. (The file owner and others permissions
are not affected by the effective rights mask; all other entries are.)
Lines 11—15 display
the default ACL associated with this directory. Directories may
have a default ACL. Regular files never have a default ACL.
The default behavior for getfacl is to display both the ACL and the
default ACL, and to include an effective rights comment for lines
where the rights of the entry differ from the effective rights.
If output is to a terminal, the effective rights comment is aligned to
column 40. Otherwise, a single tab character separates the ACL entry
and the effective rights comment.
The ACL listings of multiple files are separated by blank lines.
The output of getfacl can also be used as input to setfacl.
Options
| -b, —remove-all | Remove all extended ACL entries. The base ACL entries of the owner, group and others are retained. |
| -k, —remove-default | Remove the Default ACL. If no Default ACL exists, no warnings are issued. |
| -n, —no-mask | Do not recalculate the effective rights mask. The default behavior of setfacl is to recalculate the ACL mask entry, unless a mask entry was explicitly given. The mask entry is set to the union of all permissions of the owning group, and all named user and group entries. (These are exactly the entries affected by the mask entry). |
| —mask | Do recalculate the effective rights mask, even if an ACL mask entry was explicitly given. (See the -n option.) |
| -d, —default | All operations apply to the Default ACL. Regular ACL entries in the input set are promoted to Default ACL entries. Default ACL entries in the input set are discarded. (A warning is issued if that happens). |
| —restore=file | Restore a permission backup created by «getfacl -R» or similar. All permissions of a complete directory subtree are restored using this mechanism. If the input contains owner comments or group comments, setfacl attempts to restore the owner and owning group. If the input contains flags comments (which define the setuid, setgid, and sticky bits), setfacl sets those three bits accordingly; otherwise, it clears them. This option cannot be mixed with other options except «—test«. |
| —test | Test mode. Instead of changing the ACLs of any files, the resulting ACLs are listed. |
| -R, —recursive | Apply operations to all files and directories recursively. This option cannot be mixed with «—restore«. |
| -L, —logical | «Logical walk»: follow symbolic links to directories. The default behavior is to follow symbolic link arguments, and skip symbolic links encountered in subdirectories. Only effective in combination with -R. This option cannot be mixed with «—restore«. |
| -P, —physical | «Physical walk»: do not follow symbolic links to directories. This also skips symbolic link arguments. Only effective in combination with -R. This option cannot be mixed with «—restore«. |
| -v, —version | Print the version of setfacl, and exit. |
| -h, —help | Print a help message explaining the command line options. |
| — | A double-dash marks the end of command line options; all remaining parameters are interpreted as file names. This option is especially useful for file names that start with a dash. |
| — | If the file name parameter is a single dash, setfacl reads a list of files from standard input. |
体验4 - 备份和恢复ACL
主要的文件操作命令cp和mv都支持ACL,只是cp命令需要加上-p 参数。但是tar等常见的备份工具是不会保留目录和文件的ACL信息的。 如果希望备份和恢复带有ACL的文件和目录,那么可以先把ACL备份到一个文件里。以后用—restore选项来回复这个文件中保存的ACL信息:
# getfacl -R dir1 > dir1.acl # ls -l dir1.acl total 16 -rw-r--r-- 1 root root 310 Dec 12 21:10 dir1.acl
我们用-b选项删除所有的ACL数据,来模拟从备份中回复的文件和目录:
# setfacl -R -b dir1 # getfacl -R dir1 # file: dir1 # owner: root # group: root user::rwx group::r-x other::r-x # file: dir1/file1 # owner: root # group: root user::rw- group::r-- other::r--
现在我们从dir1.acl中恢复被删除的ACL信息:
# setfacl --restore dir1.acl # getfacl -R dir1 # file: dir1 # owner: root # group: root user::rwx group::r-x other::r-x default:user::rwx default:group::r-x default:group:testg1:rwx default:mask::rwx default:other::r-x # file: dir1/file1 # owner: root # group: root user::rw- group::r-x #effective:r-- group:testg1:rwx #effective:rw- mask::rw- other::r--
DESCRIPTION
If getfacl is used on a file system that does not support ACLs, getfacl
displays the access permissions defined by the traditional file mode permission
bits.
The output format of getfacl is as follows:
1: # file: somedir/ 2: # owner: lisa 3: # group: staff 4: user::rwx 5: user:joe:rwx #effective:r-x 6: group::rwx #effective:r-x 7: group:cool:r-x 8: mask:r-x 9: other:r-x 10: default:user::rwx 11: default:user:joe:rwx #effective:r-x 12: default:group::r-x 13: default:mask:r-x 14: default:other:--- |
Lines 4, 6 and 9 correspond to the user, group and other fields of
the file mode permission bits. These three are called the base ACL
entries. Lines 5 and 7 are named user and named group entries. Line 8 is
the effective rights mask. This entry limits the effective rights granted
to all groups and to named users. (The file owner and others permissions
are not affected by the effective rights mask; all other entries are.)
Lines 10—14 display
the default ACL associated with this directory. Directories may
have a default ACL. Regular files never have a default ACL.
The default behavior for getfacl is to display both the ACL and the
default ACL, and to include an effective rights comment for lines
where the rights of the entry differ from the effective rights.
If output is to a terminal, the effective rights comment is aligned to
column 40. Otherwise, a single tab character separates the ACL entry
and the effective rights comment.
The ACL listings of multiple files are separated by blank lines.
The output of getfacl can also be used as input to setfacl.