В ora-12560: tns в:ошибка протокола адаптер
Содержание:
- I want to customize, or make my own error messages.
- Supported eCAP versions
- Public Java methods
- Miscellaneous
- License Issues
- Стартовая страница модуля
- Is there a way to do ident lookups only for a certain host and compare the result with a userlist in squid.conf?
- Implementing an ICAP client
- Значение ошибки протокола?
- Behavior
- Configuring and run c-icap server
- Squid Configuration
- Error codes
- Журнал
- API Routing
- Configure Explicit Proxy
- Squid doesn’t match my subdomains
- Рекомендуемые ссылки для решения:
- What We Do
- The Basics: How the parts fit together
- Access Lists
- Приложение Б., «Руководство по развертыванию Symantec» Appendix B: Symantec Deployment Guide
I want to customize, or make my own error messages.
You can customize the existing error messages as described in Customizable Error Messages in SquidFaq/MiscFeatures. You can also create new error messages and use these in conjunction with the deny_info option.
For example, lets say you want your users to see a special message when they request something that matches your pornography list. First, create a file named ERR_NO_PORNO in the /usr/local/squid/etc/errors directory. That file might contain something like this:
Our company policy is to deny requests to known porno sites. If you feel you've received this message in error, please contact the support staff (support@this.company.com, 555-1234).
Next, set up your access controls as follows:
acl porn url_regex "/usr/local/squid/etc/porno.txt" deny_info ERR_NO_PORNO porn http_access deny porn (additional http_access lines ...)
Supported eCAP versions
Squid-3.1 supports libecap v0.0.3 only, but will try to build with any libecap version installed. Builds with incompatible versions should fail, but be careful: Check that you are building with libecap v0.0.3 and not the latest library version. The same applies to Squid-3.2 releases prior to v3.2.0.6.
Squid-3.2 releases starting with v3.2.0.6 support libecap v0.2.0 and have a configure-time libecap version check.
Eventually, Squid may also check (at runtime) that the loaded adapter was built with a compatible libecap version, but that check will not be possible until libecap API supports it.
Public Java methods
Given an IP-address, a port and an ICAP service name it will initialize a socket connection to the BCP. The preview size will be determined by an ‘option’ request from the BCP.
This method throws an IOException if the socket connection or IO streams cannot be started. This lets the user of the class responsible for making a decision if such an error occurs. There is no good way to solve this exception automatically.
Same as the one above, but the preview size assigned in the method call will be used to transfer files. Use this method to minimize overhead, but be sure to not change the BCP settings.
Given a filename, it will send the given file through the initialized connection to the BCP. If the file is clean it will return true and if the file is infected it will return false.
Miscellaneous
Choice for CentOS
- I decided to use CentOS whenver flexibility is required (image size ~350MB)
- Atomic Linux is used for Dnsmasq (image size ~5MB)
Security Aspects
- Each application has its own container, thus high isolation
- Applications run non-root
- VPN CA is kept in a separate Docker Volume. Password should be kept at a secure location
- VPN is using TLS 1.2 with Elliptic Curve certificates, DHE and tls-crypt channel.
Blacklist
- The blacklists can be configured by adjusting the Squid containers ENV var SQUIDGUARD_FILTER (list of space separated categories)
Cleanup
In case you want to remove the Docker containers, networks and volumes, the following steps can be used after stopping the services:
docker rm vpnbox_clamav_1 vpnbox_squid_1 vpnbox_cicap_1 vpnbox_openvpn_1 vpnbox_dnsmasq_1 docker network rm vpnbox_main docker image prune
License Issues
Note: These are not legally binding opinions. If you have any doubts regarding the licensing please contact your lawyer.
Squid is licensed under the GPLv2+, which brings up the question of licensing for distributed Squid plugins. There are several, conflicting views regarding eCAP adapter licensing requirements, including:
- eCAP is not a Squid-specific API. Compliant eCAP adapters should work in any eCAP-compliant host application. They are not «Squid plugins» just like libc is not a Squid plugin. Thus, eCAP adapter distribution is not subject to Squid licensing restrictions.
-
Communication with eCAP adapters is limited to invoking the «main» functions of the adapter and waiting for them to return. FSF considers this a borderline case:
-
eCAP modules fall well inside the boundary of code loaded and run internally. As such any modules require a GPLv2+ compatible license in order to distribute:
Стартовая страница модуля
Прокси-сервер — служба, позволяющая клиентам выполнять косвенные запросы к другим сетевым службам. Сначала клиент подключается к прокси-серверу и запрашивает какой-либо веб-ресурс, расположенный на другом сервере. Затем прокси-сервер либо подключается к указанному серверу и получает ресурс у него, либо возвращает ресурс из собственного кэша (если кто-то из клиентов уже обращался к этому ресурсу). В некоторых случаях запрос клиента или ответ сервера может быть изменён прокси-сервером в определённых целях.
Также, прокси-сервер позволяет анализировать проходящие через сервер HTTP-запросы клиентов, выполнять фильтрацию и учёт трафика по URL и mime-типам. Кроме этого, прокси-сервер реализует механизм доступа в интернет по логину/паролю.
Прокси-сервер выполняет кеширование объектов, полученных пользователями из интернета и за счёт этого сокращает потребление трафика и увеличивает скорость загрузки страниц.
При входе в модуль отображается состояние служб, кнопка «Выключить» (или «Включить» если модуль выключен) и последние сообщения в журнале.
Is there a way to do ident lookups only for a certain host and compare the result with a userlist in squid.conf?
You can use the ident_lookup_access directive to control for which hosts Squid will issue ident lookup requests.
Additionally, if you use a ident ACL in squid.conf, then Squid will make sure an ident lookup is performed while evaluating the acl even if ident_lookup_access does not indicate ident lookups should be performed earlier.
However, Squid does not wait for the lookup to complete unless the ACL rules require it. Consider this configuration:
acl host1 src 10.0.0.1 acl host2 src 10.0.0.2 acl pals ident kim lisa frank joe http_access allow host1 http_access allow host2 pals
Requests coming from 10.0.0.1 will be allowed immediately because there are no user requirements for that host. However, requests from 10.0.0.2 will be allowed only after the ident lookup completes, and if the username is in the set kim, lisa, frank, or joe.
Using Proxy Authentication
Another option is to use proxy-authentication. In this scheme, you assign usernames and passwords to individuals. When they first use the proxy they are asked to authenticate themselves by entering their username and password.
In Squid this authentication is handled via external processes. For information on how to configure this, please see SquidFaq/ProxyAuthentication.
Implementing an ICAP client
A detailed explanation of how ICAP works is beyond the scope of this
article, but a few things about ICAP are worth mentioning here to help you
fully understand how WebSphere DataPower deals with it.
ICAP is a request/response application layer protocol similar in semantics
and usage to HTTP/1.1. Methods defined by the specification for ICAP are OPTIONS,
REQMOD and RESPMOD. ICAP headers are similar to HTTP headers, but the
specification does not exactly define how a server must handle them in a
response to indicate that a virus was found. As a result, every antivirus
software
vendor has their own implementation. WebSphere DataPower SOA Appliances
started supporting ICAP with firmware level 3.5.x, but as of firmware
3.6.1, ICAP support became a selectable verb for the MultiStep pipeline
Anti-Virus action. To configure the Anti-Virus action (Figure 1), you must
specify:
-
Anti-Virus Scan Type: Select the specific parts of the message
you want WebSphere DataPower to scan (default is entire message). -
ICAP Host Type: Select the appropriate communication method
used by the antivirus vendor’s ICAP implementations. -
Remote Host Name/Port/URI: Specify the antivirus server’s
hostname (or IP address), port, and service URI parameters. -
Anti-Virus Policy: Specify the action that WebSphere
DataPower must perform when a virus is found by the antivirus
server (default is to reject the message). -
Anti-Virus Error Policy: Specify the action WebSphere
DataPower must perform when there is a communication failure
with the antivirus server (default is to reject the message).
Значение ошибки протокола?
Ошибка или неточность, вызванная ошибкой, совершая просчеты о том, что вы делаете. Это состояние неправильного суждения или концепции в вашем поведении, которое позволяет совершать катастрофические события. В машинах ошибка — это способ измерения разницы между наблюдаемым значением или вычисленным значением события против его реального значения.
Это отклонение от правильности и точности. Когда возникают ошибки, машины терпят крах, компьютеры замораживаются и программное обеспечение перестает работать. Ошибки — это в основном непреднамеренные события. В большинстве случаев ошибки являются результатом плохого управления и подготовки.
Behavior
When the FolderWatch application starts, it will add all the current files in the directory to a scan-queue. This list is iterated through when there is open for new connections. The max amount of connections is specified in the app.config as ‘maxInTransfer’. The scan-queue limit is defined in app.config as ‘maxInQueue’.
Apart from adding all current files in the directory to the scan-queue, it will also watch the directory for created files. When a file is created, it is added to the scan-queue. The maxInQueue limit ensure that system memory is not clogged with waiting files. If the scan-queue is full when a new file is added, it will be ignored.
In the app.config a ‘addAllFilesInterval’ is defined in milliseconds. When the time has passed, it will added files in the directory to the scan-queue so that they aren’t ignored completely.
The console application will print out to the command prompt with informations, error and so on. Alternatively, if it is installed as a service, it will send all messages to the system’s event log.
Configuring and run c-icap server
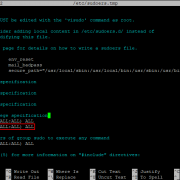
Edit c-icap.conf as follows:
PidFile /var/run/c-icap/c-icap.pid CommandsSocket /var/run/c-icap/c-icap.ctl StartServers 1 MaxServers 20 MaxRequestsPerChild 100 Port 1344 User squid Group squid ServerAdmin yourname@yourdomain TmpDir /tmp MaxMemObject 131072 DebugLevel 0 ModulesDir /usr/local/lib/c_icap ServicesDir /usr/local/lib/c_icap LoadMagicFile /usr/local/etc/c-icap.magic acl localhost src 127.0.0.1/255.255.255.255 acl PERMIT_REQUESTS type REQMOD RESPMOD icap_access allow localhost PERMIT_REQUESTS icap_access deny all ServerLog /var/log/i-cap_server.log AccessLog /var/log/i-cap_access.log
Edit paths if necessary and start c-icap server. Add startup script to your OS.
-
Note: Method OPTIONS is excluding from scanning in latest squidclamav release (starting from squidclamav version 6.14). So, permit access for it not required.
-
Note: TmpDir usually set to /var/tmp (this is default). Be very careful when change it. TmpDir uses for temp files when oblect in memory greater than MaxMemObject. And this temp files (CI_TMP_XXXX) remains in TmpDir when processing complete. Schedule housekeeping for TmpDir otherwise free space on /var filesystem can ran out on high loaded servers.
-
Note: In some cases you can increase MaxMemObject to increase performance at the cost of some increase in consumption of RAM. Sometimes it is advisable to set this parameter to the maximum value of the logical IO unit for your OS.
Squid Configuration
ICAP server configuration should be detailed in the server documentation. Squid is expected to work with any of them. The configuration of Squid-3 underwent a change between Squid-3.0 and Squid-3.1
Squid 3.1
The following example instructs Squid-3.1 to talk to two ICAP services, one for request and one for response adaptation:
icap_enable on icap_service service_req reqmod_precache bypass=1 icap://127.0.0.1:1344/request adaptation_access service_req allow all icap_service service_resp respmod_precache bypass=0 icap://127.0.0.1:1344/response adaptation_access service_resp allow all
Squid 3.0
The following example instructs Squid-3.0 to talk to two ICAP services, one for request and one for response adaptation:
icap_enable on icap_service service_req reqmod_precache 1 icap://127.0.0.1:1344/request icap_class class_req service_req icap_access class_req allow all icap_service service_resp respmod_precache 0 icap://127.0.0.1:1344/response icap_class class_resp service_resp icap_access class_resp allow all
There are other options which can control various aspects of ICAP:
CategoryFeature
Error codes
When working with the protocol, it often comes in handy to have the error codes and descriptions
| Code | Description |
|---|---|
| Informational Codes | |
| 100 | Continue After ICAP preview |
| Success codes | |
| 200 | OK |
| 204 | No modification needed |
| Client error codes | |
| 400 | Bad request |
| 403 | Forbidden |
| 404 | ICAP Service not found |
| 405 | Method not allowed for service |
| 408 | Request timeout ICAP server gave up waiting for a request from an ICAP client. |
| Server error codes | |
| 500 | Server error. Error on the ICAP server, such as «out of disk space». |
| 501 | Method not implemented. This response is illegal for an OPTIONS request since implementation of OPTIONS is mandatory. |
| 502 | Bad Gateway. This is an ICAP proxy and proxying produced an error. |
| 503 | Service overloaded. The ICAP server has exceeded a maximum connection limit associated with this service; the ICAP client should not exceed this limit in the future. |
| 505 | ICAP version not supported by server. |
Журнал
В закладке «Журнал» находится сводка всех системных сообщений от прокси-сервера. Журнал разделен на страницы, кнопками «вперед» и «назад» вы можете переходить со страницы на страницу, либо ввести номер страницы в поле и переключиться сразу на нее.
Записи в журнале выделяются цветом в зависимости от вида сообщения. Обычные сообщения системы отмечены белым цветом, сообщения о состоянии системы (включение/выключение, обработка кэша) — зеленым, ошибки — красным.
В правом верхнем углу модуля находится строка поиска. С ее помощью вы можете искать в журнале нужные вам записи.
Журнал всегда отображает события за текущую дату. Чтобы посмотреть события в другой день, выберите нужную дату, используя календарь в левом верхнем углу модуля.
API Routing
nodecap presents an expressjs-style API where middleware can be declared and matched to requests. Instead of request URI/method combinations, the unit of matching is domains through the class, which implements an efficient matcher for squid3 whitelist/blacklist syntax. Middleware is attached to handle requests to / responses from lists of domains:
Adds middleware to handle a REQMOD (HTTP request modification). The callback signature is . Calling is optional and will continue to the next handler. Be sure to have a catch-all handler at the end. can be either a DomainList instance — which allows matching request domains against a configured list — or the literal string to match all requests.
Adds middleware to handle a RESPMOD (HTTP response modification). The and options are the same as for .
Adds middleware to handle errors that occur either at the protocol level or within any options/request/response middleware.
License
The MIT License (MIT)
Copyright (c) 2014 Joseph Savona
Permission is hereby granted, free of charge, to any person obtaining a copy of
this software and associated documentation files (the «Software»), to deal in
the Software without restriction, including without limitation the rights to
use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of
the Software, and to permit persons to whom the Software is furnished to do so,
subject to the following conditions:
The above copyright notice and this permission notice shall be included in all
copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED «AS IS», WITHOUT WARRANTY OF ANY KIND, EXPRESS OR
IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS
FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR
COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER
IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN
CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
Configure Explicit Proxy
- Configuring proxy explicitly is definetly recommended. Squid bump works generally more reliable with explicit configured proxy.
- Hint: Use Foxyproxy (Firefox) or similar Proxy switcher utility, to simply turn Proxy on when VPN is enabled.
Windows VPN client
- OpenVPN on Windows is easy to use. Just copy the *.ovpn file over to C:\Program Files\OpenVPN\config (adjust if needed)
- Start OpenVPN, you will probably Admin permissions or else the Tunnel will not be properly created.
- Import Squid CA into Certificate Stores
- create file squidCA.crt with content you saved
- double click the file (info window should be presented)
- click «Install Certificate»
- pick local user as install destination
- select «Trusted Root Certification Authorities» / «Vertrauenswürdige Stammzertifizierungsstellen» as store
- Firefox uses its own Cert store (Settings -> Extended -> Certificates)
IOS
- Application & VPN Profile
- Use Itunes put the *.ovpn file in the OpenVPN Connect files. The application will then offer to import the profile
- Squid CA to prevent SSL errors
- Store CA as PEM (.crt) in Dropbox or Icloud and open the file. There should be a popup presenting the possibility to import the certificate and set it to trusted.
Verification on Client
After the tunnel has been established, make sure it is working:
Ping the VPN server:
ping 10.128.81.1
Check Transparent Proxy is working by downloading a (harmless) Eicar Test Virus
Note: Try the different variants, SSL should also work. If it works you will see a message from Squid/ClamAV, and not from your local Virus Scanner.
Squid doesn’t match my subdomains
If you are using Squid-2.4 or later then keep in mind that dstdomain acls uses different syntax for exact host matches and entire domain matches. www.example.com matches the exact host www.example.com, while .example.com matches the entire domain example.com (including example.com alone)
There is also subtle issues if your dstdomain ACLs contains matches for both an exact host in a domain and the whole domain where both are in the same domain (i.e. both www.example.com and .example.com). Depending on how your data is ordered this may cause only the most specific of these (e.g. www.example.com) to be used.
|
Squid-2.4 and later will warn you when this kind of configuration is used. If your Squid does not warn you while reading the configuration file you do not have the problem described below. Also the configuration here uses the dstdomain syntax of Squid-2.1 or earlier.. (Squid-2.2 and later needs to have domains prefixed by a dot) |
There is a subtle problem with domain-name based access controls when a single ACL element has an entry that is a subdomain of another entry. For example, consider this list:
acl FOO dstdomain boulder.co.us vail.co.us .co.us
In the first place, the above list is simply wrong because the first two (boulder.co.us and vail.co.us) are unnecessary. Any domain name that matches one of the first two will also match the last one (co.us). Ok, but why does this happen?
The problem stems from the data structure used to index domain names in an access control list. Squid uses Splay trees for lists of domain names. As other tree-based data structures, the searching algorithm requires a comparison function that returns -1, 0, or +1 for any pair of keys (domain names). This is similar to the way that strcmp() works.
The problem is that it is wrong to say that co.us is greater-than, equal-to, or less-than boulder.co.us.
For example, if you said that co.us is LESS than fff.co.us, then the Splay tree searching algorithm might never discover co.us as a match for kkk.co.us.
similarly, if you said that co.us is GREATER than fff.co.us, then the Splay tree searching algorithm might never discover co.us as a match for bbb.co.us.
The bottom line is that you can’t have one entry that is a subdomain of another. Squid will warn you if it detects this condition.
Рекомендуемые ссылки для решения:
(1)
Загрузить (компонент протокола RDP X.224 обнаружил ошибку в потоке протокола и отключил клиентскую программу.).
(2)
Компонент протокола RDP X.224 обнаружил ошибку в потоке протокола и отключил клиент.
(3) Компонент протокола RDP X.224 обнаружил ошибку в потоке протокола и отключил клиент. Идентификатор события: 50
(4) из-за ошибки протокола, обнаруженной на клиенте (код 0x1104), этот сеанс будет отключен — только для конкретных подключений с рабочего стола на сервер
(5) из-за ошибки протокола этот сеанс будет отключен. повторите попытку подключения к удаленному компьютеру
Внимание
Исправление вручную Компонент протокола RDP X.224 обнаружил ошибку в потоке протокола и отключил клиент. error only Рекомендуется только для опытных пользователей компьютеров.Загрузите инструмент автоматического ремонта вместо.
What We Do
The Institute of Chartered Accountant of Pakistan (ICAP) was established on 01 July 1961 with the prime objective of regulating the profession of accounting in Pakistan. ICAP offers great services to the nation by fostering and nurturing the young talent for leadership through its robust education and examination system throughout the years producing high calibre professionals.
In addition to this, ICAP plays its role in strengthening the regulatory framework in Pakistan through working in cooperation with important policy making institutions and regulators including the State Bank of Pakistan, the Securities and Exchange Commission of Pakistan, the Federal Board of Revenue and other Ministries.
The Basics: How the parts fit together
Squid’s access control scheme is relatively comprehensive and difficult for some people to understand. There are two different components: ACL elements, and access lists. An access list consists of an allow or deny action followed by a number of ACL elements.
When loading the configuration file Squid processes all the acl lines (directives) into memory as tests which can be performed against any request transaction. Types of tests are outlined in the next section ACL Elements. By themselves these tests do nothing. For example; the word «Sunday» matches a day of the week, but does not indicate which day of the week you are reading this.
To process a transaction another type of line is used. As each processing action needs to take place a check in run to test what action or limitations are to occur for the transaction. The types of checks are outlined in the next section Access Lists followed by details of how the checks operate.
Access Lists
There are a number of different access lists:
-
http_access: Allows HTTP clients (browsers) to access the HTTP port. This is the primary access control list.
-
http_reply_access: Allows HTTP clients (browsers) to receive the reply to their request. This further restricts permissions given by http_access, and is primarily intended to be used together with rep_mime_type acl for blocking different content types.
-
icp_access: Allows neighbor caches to query your cache with ICP.
-
miss_access: Allows certain clients to forward cache misses through your cache. This further restricts permissions given by http_access, and is primarily intended to be used for enforcing sibling relations by denying siblings from forwarding cache misses through your cache.
-
cache: Defines responses that should not be cached.
-
url_rewrite_access: Controls which requests are sent through the redirector pool.
-
ident_lookup_access: Controls which requests need an Ident lookup.
-
always_direct: Controls which requests should always be forwarded directly to origin servers.
-
never_direct: Controls which requests should never be forwarded directly to origin servers.
-
snmp_access: Controls SNMP client access to the cache.
-
broken_posts: Defines requests for which squid appends an extra CRLF after POST message bodies as required by some broken origin servers.
-
cache_peer_access: Controls which requests can be forwarded to a given neighbor (cache_peer).
-
htcp_access: Controls which remote machines are able to make HTCP requests.
-
htcp_clr_access: Controls which remote machines are able to make HTCP CLR requests.
-
request_header_access: Controls which request headers are removed when violating HTTP protocol.
-
reply_header_access: Controls which reply headers are removed from delivery to the client when violating HTTP protocol.
-
delay_access: Controls which requests are handled by what delay pool
-
icap_access: (replaced by adaptation_access in Squid-3.1) What requests may be sent to a particular ICAP server.
-
adaptation_access: What requests may be sent to a particular ICAP or eCAP filter service.
-
log_access: Controls which requests are logged. This is global and overrides specific file access lists appended to access_log directives.
Notes:
An access list rule consists of an allow or deny keyword, followed by a list of ACL element names.
An access list consists of one or more access list rules.
Access list rules are checked in the order they are written. List searching terminates as soon as one of the rules is a match.
If a rule has multiple ACL elements, it uses AND logic. In other words, all ACL elements of the rule must be a match in order for the rule to be a match. This means that it is possible to write a rule that can never be matched. For example, a port number can never be equal to both 80 AND 8000 at the same time.
To summarize the ACL logics can be described as: (note: AND/OR below is just for illustartion, not part of the syntax)
http_access allow|deny acl AND acl AND ...
OR
http_access allow|deny acl AND acl AND ...
OR
...
If none of the configured rules match, then Squid reverses the action of the last configured rule. For example, if the last configured http_access action was «allow», then Squid denies access.
Consult directive-specific documentation for that directive default behavior. For example, if no http_access rules are configured at all, Squid denies access.
Relying on these implicit defaults is dangerous because Squid action may «unexpectedly» change when you add or remove the last configured rule. It is best to end your rules with an explicit rule that will match any transaction. For example:
http_access deny all
Приложение Б., «Руководство по развертыванию Symantec» Appendix B: Symantec Deployment Guide
Поддерживается решение Symantec DLP версии 11 и новее.The supported Symantec DLP versions are 11 and higher.
Как указано выше, сервер обнаружения нужно развернуть в том же центре обработки данных Azure, что и клиент Cloud App Security.As noted above, you should deploy a detection server in the same Azure datacenter where your Cloud App Security tenant resides. Сервер обнаружения синхронизируется с сервером принудительной защиты через выделенный туннель IPSec.The detection server syncs with the enforce server through a dedicated IPSec tunnel.
Установка сервера обнаруженияDetection server installation
Сервер обнаружения, используемый Cloud App Security, представляет собой стандартный сервер с поддержкой модуля Network Prevent for Web.The detection server used by Cloud App Security is a standard Network Prevent for Web server. Вам потребуется изменить несколько параметров настройки.There are several configuration options that should be changed:
-
Отключите режим пробной версии.Disable Trial Mode:
-
В разделе системные > серверы и устройства обнаружениящелкните целевой объект ICAP.Under System > Servers and Detectors, click on the ICAP target.
-
Щелкните Настройка.Click Configure.
-
Отключение режима пробной версии.Disable Trial Mode.
-
-
В ICAPразделе > Фильтрация ответовICAP измените значение параметра игнорировать ответы меньше, чем на 1.Under ICAP > Response Filtering, change the Ignore Responses Smaller Than value to 1.
-
И добавить «Application/ * » в список » проверить тип содержимого».And add «application/*» to the list of Inspect Content Type.
-
Щелкните Сохранить.Click Save
Настройки политикиPolicy configuration
Cloud App Security свободно поддерживает все типы правил обнаружения, включенные в решение Symantec для защиты от потери данных, поэтому нет необходимости изменять существующие правила.Cloud App Security seamlessly supports all detection rule types included with Symantec DLP, so there’s no need to alter existing rules. Тем не менее, чтобы обеспечить полную интеграцию, необходимо применить изменение конфигурации ко всем существующим и новым политикам.However, there’s a configuration change that must be applied to all existing and new policies to enable full integration. Это изменение представляет собой дополнение к определенным правилам отклика для всех политик.This change is the addition of a specific response rule to all policies.
Добавьте в Vontu изменение конфигурации.Add the configuration change to your Vontu:
-
Перейдите к разделу Управление > Policies > правилами ответов на политики и нажмите кнопку Добавить правило ответа.Go to Manage > Policies > Response Rules and click Add Response Rule.
-
Установите переключатель Automated Response (Автоматический отклик) и нажмите кнопку Next (Далее).Make sure Automated Response is selected and click Next.
-
Введите имя правила, например Блокировка HTTP/HTTPS.Type a rule name, for example, Block HTTP/HTTPS. В разделе действиявыберите блокировать HTTP/HTTPS и нажмите кнопку сохранить.Under Actions, select Block HTTP/HTTPS and click Save.
Добавьте созданное правило во все существующие политики.Add the rule you created to any existing policies:
-
В каждой политике перейдите на вкладку Response (Отклик).In each Policy, switch to the Response tab.
-
В раскрывающемся списке правило ответа выберите созданное ранее правило блокировки ответов.From the Response rule drop-down, select the block response rule you created earlier.
-
Сохраните политику.Save the policy.
Это правило необходимо добавить во все существующие политики.This rule must be added to all existing policies.
Примечание
Если вы используете Symantec vontu для проверки файлов из Dropbox, то CAS автоматически отображает файл, исходя из следующего URL-адреса: http://misc/filename этот URL-адрес на самом деле не является ведущим, но используется для ведения журнала.If you use Symantec vontu to scan files from Dropbox, CAS automatically displays the file as originating from the following URL: http://misc/filename This placeholder url doesn’t actually lead anywhere but is used for logging purposes.