Wifi enterprise. freeradius + freeipa + ubiquiti
Содержание:
Предварительное ознакомление с объектом тестирования
Как уже было сказано выше, перед началом активной работы над обзором для эксперта TAdviser представителями ГК Astra Linux была проведена онлайн-презентация основных возможностей ОС Astra Linux CE, продолжавшаяся немногим меньше полутора часов. Причем, это не было каким-то VIP-мероприятием, организованным с рекламной целью – подобные презентации являются стандартным элементом коммуникации разработчиков и специалистов технической поддержки с заказчиками. График этих мероприятий весьма насыщенный – эксперту TAdviser пришлось даже провести пару дней в ожидании свободного тайм-слота.
О том, что онлайн-презентации возможностей программного продукта являются штатным элементом продвижения и технической поддержки говорил и весьма точно соблюдавшийся тайминг сессии, и последовательность демонстрации, и отработанные выступления докладчиков, сопровождавшиеся активной демонстрацией на стенде.
Приятным и полезным бонусом к онлайн-презентации стала также ее запись, которую представители группы компаний передали в распоряжение эксперта спустя пару дней после показа (см. Рис. 6). Этот ролик активно использовался экспертом в продолжение всей работы над обзором (и еще будет использован в гораздо большем объеме в дальнейшем – при подготовке второй части обзора). Причем, даже такие мелкие детали оформления ролика, как вводные титры с перечнем всех участников онлайн-сессии и таймингом записи, показывают, что это был пример именно штатной работы, а не «показательное выступление».
 Рис. 6. Начальный кадр записи онлайн-презентации ОС Astra Linux со структурой и таймингом мероприятия
Рис. 6. Начальный кадр записи онлайн-презентации ОС Astra Linux со структурой и таймингом мероприятия
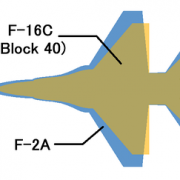
Демостенд Aquila (см. Рис. 7 – слайд из вводной презентации онлайн-сессии) представляет в миниатюре корпоративную ИТ-инфраструктуру на базе ОС Astra Linux – он содержит образцы основного системного и прикладного ПО, функционирующего в экосистеме Astra Linux:
- ПО управления идентификацией пользователей, задания политик доступа и аудита для сетей FreeIPA;
- ПО управления конфигурациями Foreman и Puppet;
- ПО мониторинга событий и статусов Zabbix;
- ПО поддержки репозитория пакетов;
- прикладное ПО (порядка двух десятков программных продуктов, адаптированных к работе в среде Astra Linux).
Подробнее о прикладном ПО, работающем под управлением Astra Linux, рассказано в подразделе «Сценарий 1.1. «Типовой госслужащий»», а о системном ПО – в подразделе «Сценарий 1.2. «Ведомственный ИТ-администратор»»
 Рис. 7. Структура демостенда Aquila с набором системного и прикладного ПО на базе ОС Astra Linux
Рис. 7. Структура демостенда Aquila с набором системного и прикладного ПО на базе ОС Astra Linux
Installing FreeIPA server
When all OS is ready and all prerequisites are met, let’s try out FreeIPA!
-
Install FreeIPA server. From root terminal, run:
- # yum install freeipa-server
- Note that the installed package just contains all the bits that FreeIPA uses, it does not configured the actual server.
-
Configure a FreeIPA server.
- The command can take command arguments or can be run in the interactive mode. You can get more details with man ipa-server-install. To start the interactive installation, run:
- # ipa-server-install
- The command will at first gather all required information and then configure all required services.
Administrative users in FreeIPA
To be able to perform any administrative task you need to authenticate to the server. During the configuration step you have been prompted to create two users. The first one Directory Manager is the superuser that needs to be used to perform rare low level tasks. For the normal administrative activity an administrative account admin has been created.
To authenticate as the admin, just run:
$ kinit admin Password for admin@IPA.TEST:
You will be prompted for the password. Use the password that you specified during the configuration step for the admin user. As a result of this operation you acquire Kerberos ticket (more info).
Help system in FreeIPA
You can use the ticket acquired as a result of the operation described above to perform different administrative tasks. The first task that we will do is add a user via command line. To do that we will first inspect the command line interface by reading man pages of the ipa command:
$ man ipa
One of the core features of IPA is its extensibility and pluggability. This means that new functionality can be added later on top of the existing, already running server. This also means that the help system i.e. man pages should be pluggable and extensible. To accommodate this requirement the ipa has a help system beyond man pages that allows addition of the information. To get more information, run:
- $ ipa help topics to get a list of help topics
- $ ipa help <topic> to print help for chosen topic
- $ ipa help <command> to dive into the details of the command or topic
Adding your first user
Run ipa help user to see help on the user operations. Keep in mind that the password management is a separate step and operation so after a user is created the password for him should be set using ipa passwd command otherwise the newly created user would not be able to authenticate.
To create a user run
ipa user-add
command with or without additional parameters. If you omit any of the required parameters or all of them the interface will prompt you for the information.
After adding user add a password for him:
ipa passwd <user>
This will create a password, but it will be a temporary one. The one that you need to change on the first authentication. This is done on purpose so that administrator can reset a password for a user but would not be able to take advantage of that knowledge since user would has to change the password on the first login.
You can now authenticate as the new user with
kinit <user>
command. This will prompt you for a password and the immediately request a password change.
Web User Interface
Next step is to try the web UI. Make sure that your administrative ticket is valid by running
kinit admin
command. Run firefox in the same command window. It will start an instance of the firefox. In the address bar type the name of the FreeIPA server machine (e.g. server.ipa.test).
As the first step the FreeIPA server via browser will ask you to accept a certificate for a secure SSL communication between your client (browser) and the server (ipa). Follow the prompts and accept the exception. Be sure that imported certificate is comes from FreeIPA server and not from attacker!
When certificate is accepted, Web UI will most likely detect that it does not have any Kerberos credentials available and will show up user and password login screen. To properly configure the browser, you can follow a link on the log in screen to run the configuration tool.
Overview
The implementation of a dynamic management of replication topology uncovered a need for an additional API for querying for a presence and status of various services (DNS, CA, KRA) on individual nodes. FreeIPA holds a list of configured services per master in the subtree.
This is however more of an implementation detail than an information readily consumable by administrators, since there is many-to-one mapping between systemd services and a high-level functionality provided by them, e.g. a FreeIPA DNS server functionality is provided by 2 systemd services set up by .
That’s why this document introduces the concept of server roles as an user-facing abstraction providing high-level information about services running on particular FreeIPA master.
Overview
When FreeIPA server is configured with Winsync synchronization with Active Directory, all users are copied to FreeIPA server with generated POSIX attributes (e.g. login name, UID, GID, shell…). Such architecture has several downsides, when compared to infrastructure based on Cross-Realm Trusts. However, it was very difficult to migrate to it given synchronized AD users already had POSIX attributes generated.
New ID Views mechanism allows configuring POSIX attributes for AD users and thus allows admin to remove such user entity from FreeIPA Directory Server, leverage Trusts and only define the default (or per host group) user (or group) POSIX attributes.
Download and unpack original images
For fast download run the following commands in terminal:
mkdir -p /tmp/vhd cd /tmp/vhd wget http://download.microsoft.com/download/5/4/C/54C15FA1-B3AA-4A8B-B26C-47C3BA7A20E0/WS2008R2Fullx64Ent.part01.exe wget http://download.microsoft.com/download/5/4/C/54C15FA1-B3AA-4A8B-B26C-47C3BA7A20E0/WS2008R2Fullx64Ent.part02.rar wget http://download.microsoft.com/download/5/4/C/54C15FA1-B3AA-4A8B-B26C-47C3BA7A20E0/WS2008R2Fullx64Ent.part03.rar unar WS2008R2Fullx64Ent.part01.exe # OR if unar is not available unrar x WS2008R2Fullx64Ent.part01.exe
Self-Managed Tokens
Software Tokens
Adding a token is easy. If you are logged in as , you can create a self-managed software token by running . Alternatively, you can do this via the UI: OTP Tokens -> Add. After adding the token via either method, simply scan the QR code with FreeOTP.
Now your token is provisioned. Try to log in (). Remember to enter both your password and your token code (in the form <password><token code>). This should work without problem. Now, try to log in again with the same password and token code. This should fail since the OTP code was already used.
Feel free to add, edit and delete as many tokens as you’d like. You can try this with both HOTP and TOTP tokens. Notice that you are not permitted to remove the last active token.
Programmable Hardware Tokens
This test will require a YubiKey token.
Because of browser limitations, this command is only available on the CLI. Insert your YubiKey token and run: . If your YubiKey has an empty slot, the command will pick it automatically. Otherwise, you will need to use the argument to choose a slot to overwrite.
This token should work exactly the same as a software token in the previous example. All the same policy should apply.
Install FreeIPA Server CentOS 7
First of all let us search the package name required for configuring FreeIPA server.
# yum search ipa-server Loaded plugins: fastestmirror, langpacks Loading mirror speeds from cached hostfile * base: ftp.iitm.ac.in * extras: centos.mirrors.estointernet.in * updates: centos.mirrors.estointernet.in ================================================= N/S matched: ipa-server ================================================= ipa-server.x86_64 : The IPA authentication server ipa-server-common.noarch : Common files used by IPA server ipa-server-dns.noarch : IPA integrated DNS server with support for automatic DNSSEC signing ipa-server-trust-ad.x86_64 : Virtual package to install packages required for Active Directory trusts Name and summary matches only, use "search all" for everything.
So now we know we need and rpm to set up our FreeIPA server.
# yum install ipa-server.x86_64 ipa-server-dns.noarch -y
Once installed, update your hosts file with the FQDN names of all the nodes in your setup. Without this the FreeIPA server configuration will not work.
# cat /etc/hosts 127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4 ::1 localhost localhost.localdomain localhost6 localhost6.localdomain6 10.0.2.31 node2.example.com node2 10.0.2.30 node1.example.com node1 10.0.2.32 node3.example.com node3
FusionDirectory
Поскольку доступ к исходному коду GOsa для тех, кто не имеет отношения к компании Gonicus GmbH, был затруднен, разработчики приняли решение о создании более открытого и полностью поддерживаемого сообществом форка для привлечения сторонних специалистов, а также обеспечения условий для написания плагинов под большее количество приложений. Новый проект получил название FusionDirectory. Разработчики обещали не только создать самое «мощное и универсальное» решение для управления, имеющее более удобные инструменты для разработки, но и усовершенствовать документацию. В октябре 2011-го вышла версия FusionDirectory 1.0.2, но, так как работа над проектом началась совсем недавно, о каких-то особых функциональных отличиях от GOsa пока говорить не приходится. Документация, по сути, состоит из пары руководств, но, учитывая родство с GOsa, на стадии ознакомления с FusionDirectory можно использовать документацию на родительский проект. Четко определен список поддерживаемых дистрибутивов (Debian, CentOS 5/RHEL 5, Fedora 14/15, openSUSE 11.3/11.4, SLES 11), и, главное, для каждого из них создан репозиторий, обеспечивающий простую установку.
Verify FreeIPA Server
After the FreeIPA installation, authenticate to the Kerberos realm to ensure that the administrator is configured correctly.
kinit admin
If FreeIPA is working properly, the above command will prompt you for the IPA admin password. Enter the IPA admin password you set during the installation process and then press Enter.
After entering the password, you should get shell prompt.
Next, verify the FreeIPA server functionality by searching IPA user.
ipa user-find admin
Output:
-------------- 1 user matched -------------- User login: admin Last name: Administrator Home directory: /home/admin Login shell: /bin/bash Principal alias: admin@ITZGEEK.LOCAL UID: 382200000 GID: 382200000 Account disabled: False ---------------------------- Number of entries returned 1 ----------------------------
External identities for login form
yum install mod_intercept_form_submit -y
curl -Lo /etc/httpd/conf.d/wikiapp_form_submit.conf 'http://fedorapeople.org/cgit/adelton/public_git/CGI-sessions.git/plain/intercept_form_submit.conf?id=intercept-form-submit' service httpd restart
With /etc/pam.d/wikiapp in place and mod_intercept_form_submit, the application will see REMOTE_USER populated whenever the authentication via the PAM stack succeeds.
If it fails, the application will still have a chance to run local authentication.
Test with ipa hbacrule-remove-user and ipa hbacrule-add-user that the authentication using the mod_intercept_form_submit, observes the access control just like mod_authnz_pam does for Kerberos. In fact, mod_intercept_form_submit is calling mod_authnz_pam internally.
Note that we configure the module on /application/login2 because with Kerberos on /application/login, that is where the for submission will run. If we omitted the Kerberos configuration, we would want mod_intercept_form_submit configured on /application/login.
3rd party Applications Integration
DisclaimerNote that these are community provided HOWTOs and we cannot guarantee that all work against the newest and greatest version of FreeIPA. If you hit any issue, please, .
Mail Services
- Dovecot Integration
- Dovecot IMAPS Integration with FreeIPA using Single Sign On
- Zimbra Collaboration Server 7.2 Authentication and GAL lookups against FreeIPA
Web Services
- Setting up MediaWiki to run against FreeIPA
- LDAP authentication for Atlassian JIRA using FreeIPA
- Setting up Redmine to authenticate users against FreeIPA
- Setting up Rhodecode to authenticate users against FreeIPA
- Setting up The Bug Genie to authenticate users against FreeIPA
Virtualization
- Authenticating libvirt (with VNC) against IPA
- vSphere 5 integration
OpenShift
- OpenShift Broker and IPA DNS Server with Dynamic Updates with GSS-TSIG
- OpenShift Broker Apache + mod_auth_kerb for IdM
- OpenShift Enterprise on top of a trust between IPA/IdM and Windows Active Directory
OpenStack
Keystone integration with IdM (FreeIPA)
Certificates
- Implementing SNI on Apache with IPA for certificate management and Kerberos Authentication
- Using FreeIPA CA for Puppet
- Recovering from expired CA subsystem certificates in IPA 2.x
- Promoting a self-signed IPA CA
- CA Certificate Renewal
- Promoting a CA to Renewal and CRL Master
Client certificate authentication with LDAP
Authentication
- Creating a binddn for Foreman
- YubiRadius integration with group-validated FreeIPA Users using LDAPS
- Integration with Okta SSO
- Using FreeIPA and FreeRadius as a RADIUS based software token OTP system with CentOS/RedHat 7
- Using Yubikey 4 Nano to authenticate to FreeIPA enrolled host
Storage
- NetApp integration in a mixed environment
- NexentaStor integration in a mixed environment
- Integrating a Samba File Server With IPA
- Integrating Dell EMC Unity with IPA
- Integrating Dell EMC Isilon OneFS with IPA
___
How to add an HowTo on this wiki
Opening the Firewall for IPA traffic
In firewall D, we have this notion of services. If we use firewall-cmd—get-services, then we get a list of all services that are available. There are some services that involve IPA, and that is freeipa-ldap and freeipa-ldaps. These services have a backing XML file, and you will find it in /usr/lib/firewalld/services.
# cd /usr/lib/firewalld/services # ls freeipa-* freeipa-ldaps.xml freeipa-ldap.xml freeipa-replication.xml freeipa-trust.xml
So if you look at the contents of , now we can see that it is opening this list of ports. If you compare that to the list of ports we were asked to open while installing the IPA server, then you can see that most of the ports are already in there.
Below are the list of ports which must be opened for FreeIPA server
TCP Ports:
* 80, 443: HTTP/HTTPS
* 389, 636: LDAP/LDAPS
* 88, 464: kerberos
* 53: bind
UDP Ports:
* 88, 464: kerberos
* 53: bind
* 123: ntp
Let us add all the required service in the firewalld to open the ports needed by FreeIPA
# firewall-cmd --permanent --add-service freeipa-ldap success # firewall-cmd --permanent --add-service freeipa-ldaps success # firewall-cmd --permanent --add-service dns success
Now let us make our changes persistent
# firewall-cmd --reload success
Verify the firewall rules which we have just added.
# firewall-cmd --list-all public (active) target: default icmp-block-inversion: no interfaces: eth0 eth1 sources: services: ssh dhcpv6-client freeipa-ldap freeipa-ldaps dns ports: protocols: masquerade: no forward-ports: source-ports: icmp-blocks: rich rules: